This post mainly introduces the ISCSI, including its definition, main components, use and performance, as well as the limits. You will have a comprehensive understanding of it after reading the article.
What Is ISCSI
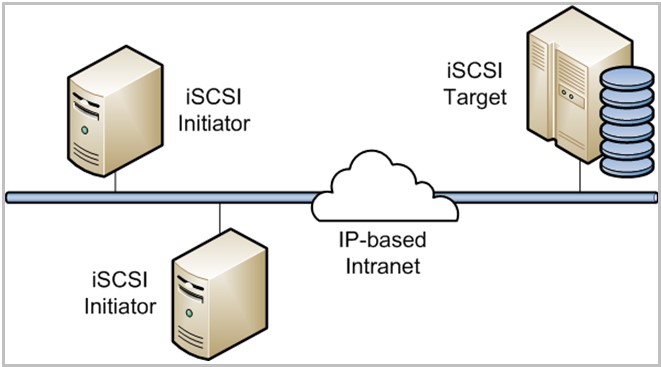
The ISCSI is short for Internet Small Computer System Interface. It is a block protocol for storage networking and runs SCSI storage protocol via a network connection (typically the Ethernet). It can help you enable block-level SCSI data transport between the ISCSI initiator and the storage target over TCP/IP networks.
The ISCSI is often used to boost data transfer over intranets and to manage storage via long distances. For instance, you can use it to transmit data over local area networks (LANs), wide area networks (WANs) and the Internet.
-image from unixmen.com
It can encrypt the network packets and decrypt when it arrives the destination. Besides, it also can help you enable location-independent data storage and retrieval. The ISICSI protocol plays a vital role in many different network configurations.
Recommended article: What Is Fibre Channel Arbitrated Loop and How’s It Working
What Consists of ISCSI
Here are two main components of ISCSI: ISCSI Initiator and ISCSI Target. The following content will talk them separately so that you can understand them better.
ISCSI Initiator
The client in the ISCSI storage network is called ISCSI initiator (node). The ISCSI initiator can connect to server (ISCSI target). By doing so, the ISCSI initiator will send SCSI commands to the ISCSI target. Due to this reason, these commands usually are contained in IP packets.
Both the ISCSI hardware initiator and ISCSI software initiator are available for you. Since boot from ISCSI is not a standard way, you can use the ISCSI software initiator as you like. Thanks to some extra configuration effort, booting from the network with the ISCSI software initiator becomes possible.
Compare with ISCSI hardware initiator, the ISCSI software initiator is less expensive. And the ISCSI software initiator is widely distributed and stable.
ISCSI Target
The server in ISCSI storage network is often called ISCSI target (node). The ISCSI target can offer you one or more so-called logical units (LUs). The LUN you see is often used for the term logical unit, which indicates the LU number actually.
The Use and Performance of ISCSI
When you need to use ISCSI instead of other protocols like Fibre Chanel? You should pick ISCSI in the situations below.
- If you don’t have much budgets for the network, the SCSI is a great choice. That is because the ISCSI can connect application servers to the shared storage without any money-consuming hardware or cabling.
- If you would like to connect multiple hosts to a single storage target, you should pick the ISCSI. The support ratio of Fibre Channel is 4:1 to 20: 1, while the support ratio of ISCSI is much higher than that.
- If you don’t have technical professionals, the ISCSI is more suitable for you. The Fibre Channel SAN requires admins with specialized skillsets. On the contrary, the ISCSI SAN can run on the existed Ethernet networks. And the common IT worker are able to install and run them by following the related guide.
How much do you know about its performance? If you are not clear, please read this with attention. The performance of ISCI is highly decided by the underlying technologies such as 10 Gigabit Ethernet (10 GbE) and bridging technology in the data center.
Of course, other elements can also affect the performance of the ISCSI. For instance, the multipathing and Jumbo frames can also have impact on the ISCSI’s performance.
The Limits of ISCSI
As you know, the ISCSI can offer you much convenience. However, it also has some limits in itself. Though deploying ISCSI is not very hard especially under the help of software-defined protocols, you are required to execute other operations when configuring the initiator and target.
Besides, as ISCSI is prone to packet sniffing, the security is annoying. Packet sniffing is the cyberattack that you may encounter when moving across a vulnerable network. Given to that fact, you need to take some measures when utilizing ISCSI. For example, skip additional security measures or simply the ISCSI management.
The Bottom Line
As you can learn from the above content, the ISCSI has many advantages but it also has some disadvantages. Fortunately, its advantages surpass the disadvantages. What’s more, you can take some actions to avoid the drawbacks. So, you can enjoy the ISCSI service without much concern.